Encryption software open source – In today’s digitally driven world, data security is paramount. Protecting sensitive information from unauthorized access is crucial for individuals and organizations alike. Encryption software plays a vital role in achieving this, and the open-source community offers a wealth of robust and reliable options. This comprehensive guide delves into the world of open-source encryption software, exploring its benefits, functionalities, and considerations for choosing the right solution for your needs.
We will cover various aspects, including different encryption algorithms, key management, and the importance of open-source principles in enhancing security and trust.
Understanding Encryption and its Importance: Encryption Software Open Source
Encryption is the process of converting readable data (plaintext) into an unreadable format (ciphertext) using a cryptographic algorithm and a key. Only those possessing the correct decryption key can revert the ciphertext back to its original form. This process safeguards sensitive data during transmission and storage, protecting it from interception or unauthorized access. The strength of encryption relies heavily on the algorithm’s complexity and the security of the key.
Types of Encryption
- Symmetric Encryption: Uses the same key for both encryption and decryption. Examples include AES (Advanced Encryption Standard) and DES (Data Encryption Standard). It’s faster but requires secure key exchange.
- Asymmetric Encryption (Public-Key Cryptography): Employs two keys: a public key for encryption and a private key for decryption. RSA and ECC (Elliptic Curve Cryptography) are common examples. It’s slower but simplifies key exchange.
- Hashing: Creates a one-way function, transforming data into a fixed-size hash value. While not strictly encryption (it cannot be reversed), it’s crucial for data integrity verification. SHA-256 and SHA-3 are popular hashing algorithms.
Exploring Popular Open-Source Encryption Software
Numerous open-source projects provide powerful encryption capabilities. Choosing the right one depends on your specific requirements, technical expertise, and the type of data you need to protect. Here are some prominent examples:
1. GPG (GNU Privacy Guard), Encryption software open source
GPG is a widely used open-source implementation of the OpenPGP standard, primarily for email encryption and digital signatures. It supports symmetric and asymmetric encryption, allowing for secure communication and data protection. GPG is known for its flexibility and extensive features, making it a versatile choice for various encryption needs. https://www.gnupg.org/
2. OpenSSL
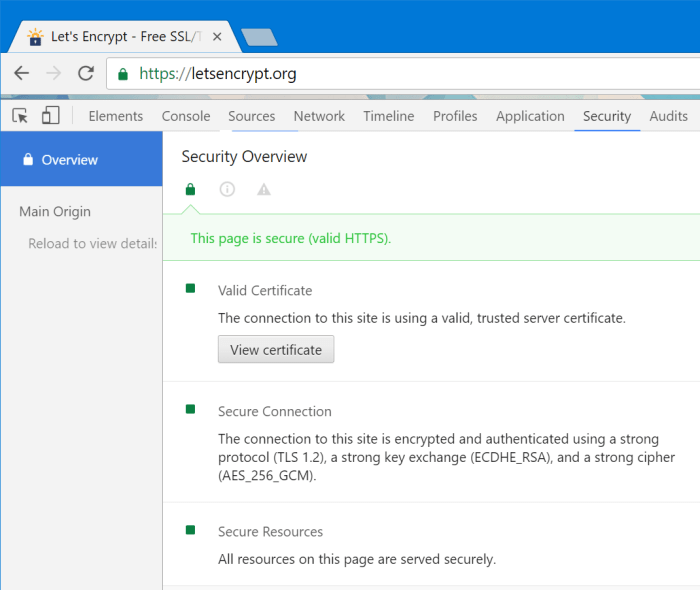
OpenSSL is a comprehensive cryptographic library offering a wide range of functionalities, including encryption, decryption, digital signatures, and certificate management. It forms the backbone of many secure communication protocols and applications. While not a standalone encryption tool, it’s a fundamental component in numerous open-source projects. https://www.openssl.org/
3. VeraCrypt
VeraCrypt is a disk encryption software based on TrueCrypt, offering strong encryption for entire disks, partitions, or files. It’s user-friendly and provides a robust solution for protecting sensitive data on your computer. It’s praised for its ease of use and security features. https://veracrypt.fr/en/
4. LUKS (Linux Unified Key Setup)
LUKS is a disk encryption standard commonly used in Linux distributions. It provides a framework for managing encryption keys and offers features like multiple key slots for enhanced security. It’s integrated into many Linux systems and provides a robust solution for whole-disk encryption. https://en.wikipedia.org/wiki/Linux_Unified_Key_Setup
Key Management: The Cornerstone of Encryption Security
The security of any encryption system hinges on the proper management of encryption keys. Losing or compromising a key renders the encrypted data inaccessible or vulnerable. Open-source encryption software often incorporates features to aid in secure key management:
- Key Generation: Robust algorithms are used to generate cryptographically strong keys.
- Key Storage: Secure methods are employed to store keys, often involving password protection or hardware security modules (HSMs).
- Key Rotation: Regularly updating keys enhances security by minimizing the impact of a potential compromise.
- Key Backup: Creating backups of keys is essential to prevent data loss in case of key compromise or system failure.
Benefits of Open-Source Encryption Software
Choosing open-source encryption offers several advantages:
- Transparency: The source code is publicly available, allowing independent security audits and verification of its integrity.
- Community Support: A large community contributes to bug fixes, improvements, and ongoing development.
- Flexibility and Customization: Open-source software can often be adapted to specific needs and integrated into existing systems.
- Cost-Effectiveness: Open-source software is typically free to use, reducing costs associated with licensing.
Choosing the Right Open-Source Encryption Software
Selecting the appropriate software depends on several factors:

Source: privacy.net
- Your technical expertise: Some solutions are more user-friendly than others.
- The type of data you need to protect: Whole-disk encryption differs from file encryption.
- Your operating system: Compatibility is crucial.
- Security requirements: The level of security needed will influence your choice.
Frequently Asked Questions (FAQ)
- Q: Is open-source encryption software as secure as commercial solutions? A: Yes, many open-source encryption solutions are considered highly secure, especially those that have undergone extensive community scrutiny and auditing.
- Q: How do I choose a strong encryption algorithm? A: AES-256 is currently considered a very strong and widely used symmetric encryption algorithm. For asymmetric encryption, ECC (Elliptic Curve Cryptography) is often preferred for its efficiency.
- Q: What is the importance of key management? A: Proper key management is paramount. Losing or compromising your encryption key renders your encrypted data useless or vulnerable.
- Q: Are there any risks associated with using open-source encryption? A: While generally safe, using poorly maintained or lesser-known open-source solutions can pose risks. Always choose reputable projects with active communities and regular updates.
- Q: Can I encrypt my entire hard drive with open-source software? A: Yes, solutions like VeraCrypt and LUKS allow for full-disk encryption.
Conclusion
Open-source encryption software provides a powerful and reliable way to protect your sensitive data. By understanding the various options, their functionalities, and the importance of key management, you can make an informed decision to safeguard your information effectively. Remember to choose reputable software, stay updated with security patches, and follow best practices for key management to maximize your data security.
Call to Action
Explore the open-source encryption options discussed in this guide and choose the solution that best suits your needs. Start protecting your valuable data today!
Essential FAQs
What are the key benefits of using open-source encryption software?
Key benefits include transparency (allowing independent security audits), community-driven development (leading to quicker bug fixes and improvements), and customization options tailored to specific needs.
Are open-source encryption tools as secure as commercial options?
The security of both open-source and commercial tools depends on their design, implementation, and ongoing maintenance. Well-maintained and actively developed open-source options can be equally secure, if not more so, due to the scrutiny from the broader community.

Source: techviral.net
How can I determine the trustworthiness of an open-source encryption project?
Look for projects with a large and active community, a long history of development, regular security audits, and transparent release processes. Check for independent security reviews and assess the overall maturity and stability of the software.
Source: codinghorror.com
What are some examples of popular open-source encryption software?
Several exist, and specific recommendations depend on the application. Research is needed to find the best fit for your specific needs. It is important to always research and select software based on reputable sources and community reviews.
