Software to protect data – In today’s digital landscape, data security is paramount. From individual users to multinational corporations, the risk of data breaches and cyberattacks is ever-present. Protecting sensitive information requires a multi-layered approach, and robust data protection software plays a crucial role in this strategy. This comprehensive guide explores various types of data protection software, their functionalities, and how they contribute to a robust security posture.
Source: 800-tech.com
We’ll delve into key features, considerations for selection, and best practices for implementation.
Understanding the Need for Data Protection Software
The escalating frequency and sophistication of cyber threats necessitate proactive measures to safeguard valuable data. Data breaches can lead to significant financial losses, reputational damage, legal repercussions, and the compromise of sensitive personal information. Data protection software acts as a critical defense mechanism, mitigating these risks by implementing various security controls. These controls range from basic access control to advanced encryption and threat detection.
Types of Data Loss
Before diving into specific software, understanding the types of data loss is essential. This helps in choosing the right tools for your specific needs. Common types include:
- Accidental Deletion: Human error leading to unintentional data deletion.
- Malware Attacks: Viruses, ransomware, and other malicious software encrypting or stealing data.
- Hardware Failure: Physical damage or malfunction of storage devices.
- Natural Disasters: Events like floods or fires that destroy data storage infrastructure.
- Insider Threats: Malicious or negligent actions by employees or insiders.
- Phishing and Social Engineering: Tricking users into revealing sensitive information.
Types of Data Protection Software: Software To Protect Data
The market offers a wide array of data protection software, each designed to address specific security challenges. Here are some key categories:
1. Antivirus and Antimalware Software
This is the first line of defense against malicious software. These programs scan files and systems for viruses, Trojans, worms, and other threats, preventing them from infecting your devices and stealing or damaging data. Examples include Norton, McAfee, and Bitdefender. These often include features like real-time protection, scheduled scans, and firewall capabilities.
2. Endpoint Detection and Response (EDR) Solutions, Software to protect data
EDR solutions go beyond traditional antivirus by actively monitoring endpoints (computers, laptops, mobile devices) for suspicious activities. They can detect and respond to advanced threats that traditional antivirus might miss. EDR provides detailed insights into potential breaches, allowing for faster remediation. Examples include CrowdStrike Falcon and Carbon Black.
3. Data Loss Prevention (DLP) Software
DLP software prevents sensitive data from leaving the organization’s control. It monitors data movement, identifies confidential information (credit card numbers, social security numbers, etc.), and blocks unauthorized access or transfer. DLP solutions can be implemented on endpoints, networks, and cloud platforms. Examples include Symantec DLP and Microsoft Azure Information Protection.
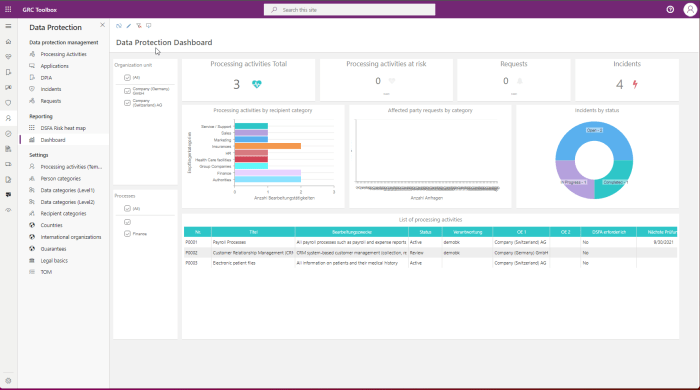
Source: swissgrc.com
4. Backup and Disaster Recovery (BDR) Solutions
BDR software creates regular backups of critical data, ensuring business continuity in case of data loss due to hardware failure, natural disasters, or cyberattacks. These solutions often include features like data replication, offsite storage, and automated recovery processes. Examples include Acronis Cyber Protect and Veeam Backup & Replication.
5. Encryption Software
Encryption converts data into an unreadable format, protecting it from unauthorized access even if it’s stolen. Encryption software can be used to protect individual files, entire hard drives, or data in transit. Common encryption methods include AES and RSA. Tools like VeraCrypt and BitLocker provide robust encryption capabilities.
6. Security Information and Event Management (SIEM) Systems
SIEM systems collect and analyze security logs from various sources, providing a centralized view of security events across an organization’s infrastructure. They can detect anomalies, identify potential threats, and facilitate incident response. Examples include Splunk and IBM QRadar.
Choosing the Right Data Protection Software
Selecting the appropriate software depends on various factors, including:
- Budget: Software solutions range from free antivirus programs to expensive enterprise-grade security suites.
- Type of Data: The sensitivity and volume of data dictate the level of protection required.
- Infrastructure: On-premises, cloud-based, or hybrid deployments influence software choices.
- Compliance Requirements: Industries like healthcare and finance have stringent data protection regulations.
- Technical Expertise: Some solutions require specialized skills to manage and maintain.
Best Practices for Data Protection
Effective data protection requires a holistic approach that goes beyond simply installing software. Here are some key best practices:
- Regular Software Updates: Keep all software, including operating systems and applications, updated with the latest security patches.
- Strong Passwords: Use complex, unique passwords for all accounts and enable multi-factor authentication wherever possible.
- Employee Training: Educate employees about phishing scams, social engineering tactics, and safe internet practices.
- Access Control: Implement strict access control measures, granting only necessary permissions to users and systems.
- Data Backup and Recovery Plan: Establish a comprehensive backup and recovery plan to ensure business continuity in case of data loss.
- Regular Security Audits: Conduct regular security assessments to identify vulnerabilities and improve security posture.
Frequently Asked Questions (FAQ)
Q: What is the best data protection software?
A: There’s no single “best” software. The ideal choice depends on your specific needs and budget. Consider factors like the type of data you need to protect, your infrastructure, and compliance requirements.
Q: Is free antivirus software sufficient?
A: Free antivirus software offers basic protection, but it may lack advanced features like real-time protection, threat intelligence, and proactive threat detection found in paid solutions. For critical data, a more comprehensive solution is often recommended.
Q: How often should I back up my data?
A: The frequency of backups depends on the criticality of your data. For critical data, daily or even more frequent backups may be necessary. For less critical data, weekly or monthly backups might suffice.
Q: What is ransomware, and how can I protect myself?
A: Ransomware is a type of malware that encrypts your files and demands a ransom for their release. Protection involves using robust antivirus software, regularly backing up your data, and avoiding suspicious links and attachments.
Q: How can I protect my data in the cloud?
A: Cloud data protection requires a multi-layered approach, including encryption, access controls, regular backups, and robust security monitoring. Choose cloud providers with strong security track records and utilize their built-in security features.
Conclusion
Protecting data is an ongoing process that requires vigilance and a comprehensive strategy. By understanding the various types of data protection software, implementing best practices, and staying informed about emerging threats, you can significantly reduce your risk of data breaches and maintain a robust security posture. Investing in the right data protection software is a critical step towards safeguarding your valuable information.

Source: gecomputers.com
References
- National Institute of Standards and Technology (NIST)
- Cybersecurity and Infrastructure Security Agency (CISA)
- European Union Agency for Cybersecurity (ENISA)
Call to Action
Start protecting your valuable data today! Explore the data protection software options available and choose the solution that best fits your needs. Don’t wait until it’s too late – proactive data protection is essential in today’s digital world.
Questions Often Asked
What is the difference between antivirus and anti-malware software?
Antivirus software primarily focuses on detecting and removing viruses, while anti-malware software has a broader scope, encompassing various types of malicious software, including spyware, Trojans, and ransomware.
How often should I update my data protection software?
Regular updates are crucial. Most software providers offer automatic updates, but it’s advisable to check for updates periodically and ensure all components are current to benefit from the latest security patches and features.
What is data encryption and why is it important?
Data encryption converts data into an unreadable format, protecting it from unauthorized access. It is vital for safeguarding sensitive information both in transit and at rest.
Can data protection software prevent all data breaches?
No software is foolproof. While data protection software significantly reduces the risk of breaches, a multi-layered approach combined with other security measures is essential for comprehensive protection.
